Cyber Crime News
-
Bank Hacking Attack Uncovered in Philippines
May 27, 2016
Symantec Security Response has learned of another Lazarus SWIFT bank hacking attack. This time the victim is a bank in the Philippines. Previous banks attacked include Banco del Austro in [...]
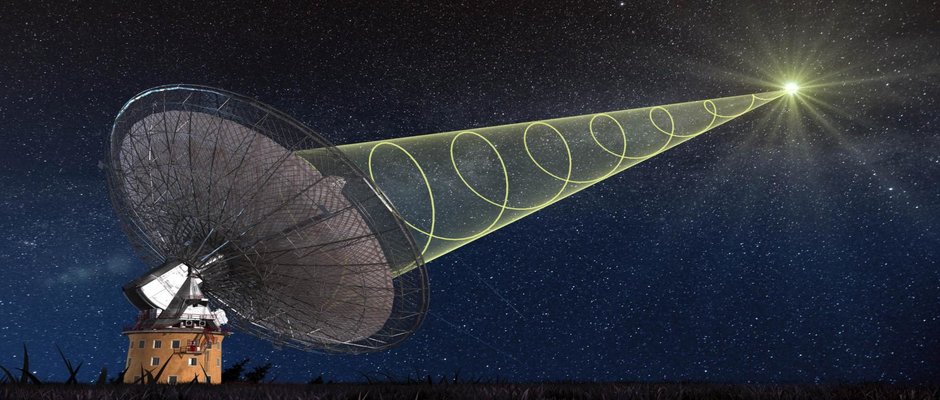
Cyberwar
-
Cyber Warfare
October 6, 2015
It feels like science fiction. Still, after all these years, it feels like sceince fiction. Cyber Warfare. Yet, this concept which comes so easy to us when we think of movies, has little grasp in the [...]
Social Network Hacking
-
Ava is supposed to “test” how employees fight off social engineering – by tricking them and stalking their social networks. The implications are [...]
-
We use it every day, it is an integral part of our lives and for more than a decade now, it has grown to become as important to us as the coffee in the morning [...]